Proton updates protest privacy guide, recommends Mail and VPN
Proton published an updated how to guide on protecting privacy at protests on Mar 3, 2026, the latest in a series of updates dating back to 2020. The guide names concrete risks, recommends a 10 digit passcode at minimum, and promotes Proton services as part of the toolkit.
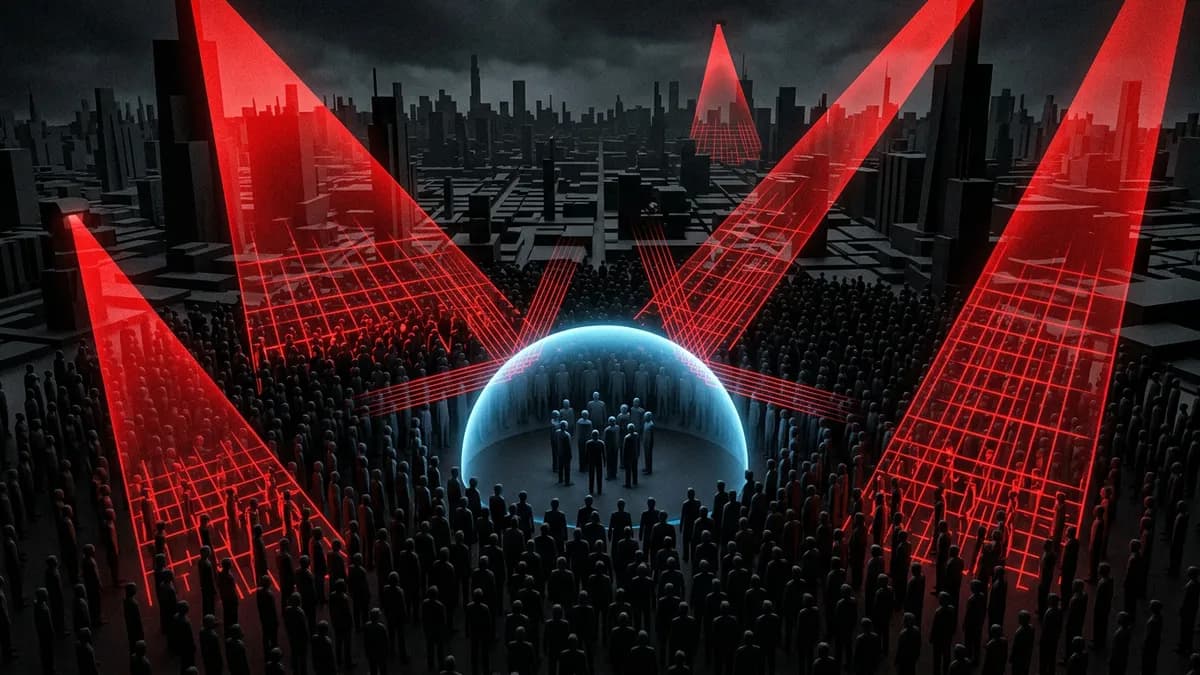
Before this update, advice for protesters oscillated between operational security checklists and ad hoc app recommendations. Tech platforms, mobile operating systems, and law enforcement tools have changed since 2020, raising new metadata and device level risks. Meanwhile high profile surveillance deployments, such as the reported "thousands" of CCTV cameras with facial recognition in Hong Kong, show how physical sensors and digital traces combine.
The scope of the threat
Proton lays out both digital and physical attack surfaces for demonstrators, from ubiquitous platform telemetry to dedicated surveillance tools. The guide warns about messaging apps, phone identifiers, location signals, and third party data brokers, and names Apple, Google, and Facebook/WhatsApp among the ecosystem actors that shape data flows. It also flags offline tools and past incidents in Minneapolis, Munich, Tehran, and Hong Kong to show how wide the risks are.
Proton is explicit about concrete mitigations. The company recommends a passcode of at least ten digits, advises minimising casual app telemetry, and offers private mail and routing tools as practical countermeasures. The guide also reiterates Proton's public position of political neutrality, writing "we are politically neutral" while arguing for privacy as a civil right. The implication is clear, Proton positions its services as operationally useful for high-risk communications, not as a political actor.
This squares with how privacy teams now plan incident communications, where metadata and device signals matter as much as message content. The guide therefore shifts focus from purely selective app choices to combined device hygiene, secure email, and network routing.
Proton's positioning and trade offs
Proton frames Proton Mail and Proton VPN as core tools in the recommended stack. That is a pragmatic move; encrypted email removes a common single point of leakage and a VPN can obscure network level metadata during travel to and from protests. These are operationally sensible choices when compared with standard platform messaging, but they carry trade offs.
Encrypted mail and VPNs increase complexity and require user discipline. Teams must manage recovery keys, trust boundaries, and device configuration, and they must accept slower workflows than default consumer apps. Proton's guide does not promise a turnkey fix. It expects users to change habits and tolerate extra friction for meaningful reductions in exposure.
For organisations evaluating options, the key decision is trade off management, not ideology. If your incident response relies on ease of use, the extra setup cost will matter. If legal exposure or staff safety is the priority, encrypted email and VPN routing become essential tools.
Why this matters
Proton updated this guide at a moment when European policy debates are tilting toward protecting encryption, yet identity and age verification proposals still threaten to create new data collection points. For comms and security teams that operate in protest-prone contexts, the update makes an operational claim: default Apple, Google, or Facebook services leave actionable traces that need independent controls. Any team that currently coordinates protest logistics over standard platform messaging should now evaluate encrypted mail and VPN routing as part of the baseline security posture.
SOURCES
https://proton.me/blog/how-to-protect-privacy-at-protests
https://yawnbox.eu/blog/how-to-use-an-ipad-as-a-secure-calling-and-messaging-device/
Share this article
Ready to Switch to EU Alternatives?
Explore our directory of 400+ European alternatives to US tech products.
Browse Categories